When someone joins or leaves your team, your identity provider (Okta, Azure AD, Authentik, etc.) can push that change directly to Speckle. Speckle’s SCIM 2.0 endpoint creates new workspace members, keeps their emails and display name in sync, and removes them from the workspace when they’re deprovisioned upstream — no manual invite or cleanup required.Documentation Index
Fetch the complete documentation index at: https://docs.speckle.systems/llms.txt
Use this file to discover all available pages before exploring further.
SCIM is available on Speckle Cloud and is currently rolling out per workspace.
Contact us to enable it on yours.
Set up SSO first
We strongly recommend setting up SSO before enabling SCIM. SSO and SCIM are independent features that solve different problems:- SSO handles login — members sign in to Speckle through your identity provider.
- SCIM handles lifecycle — your identity provider creates, updates, and removes workspace members.
Prerequisites
- SSO configured on the workspace (strongly recommended — see above).
- Workspace admin role.
- At least one verified workspace domain. SCIM only syncs emails on verified domains.
- The Speckle team has enabled SCIM on your workspace.
Enable SCIM
Configure SCIM under Workspace Settings → Security.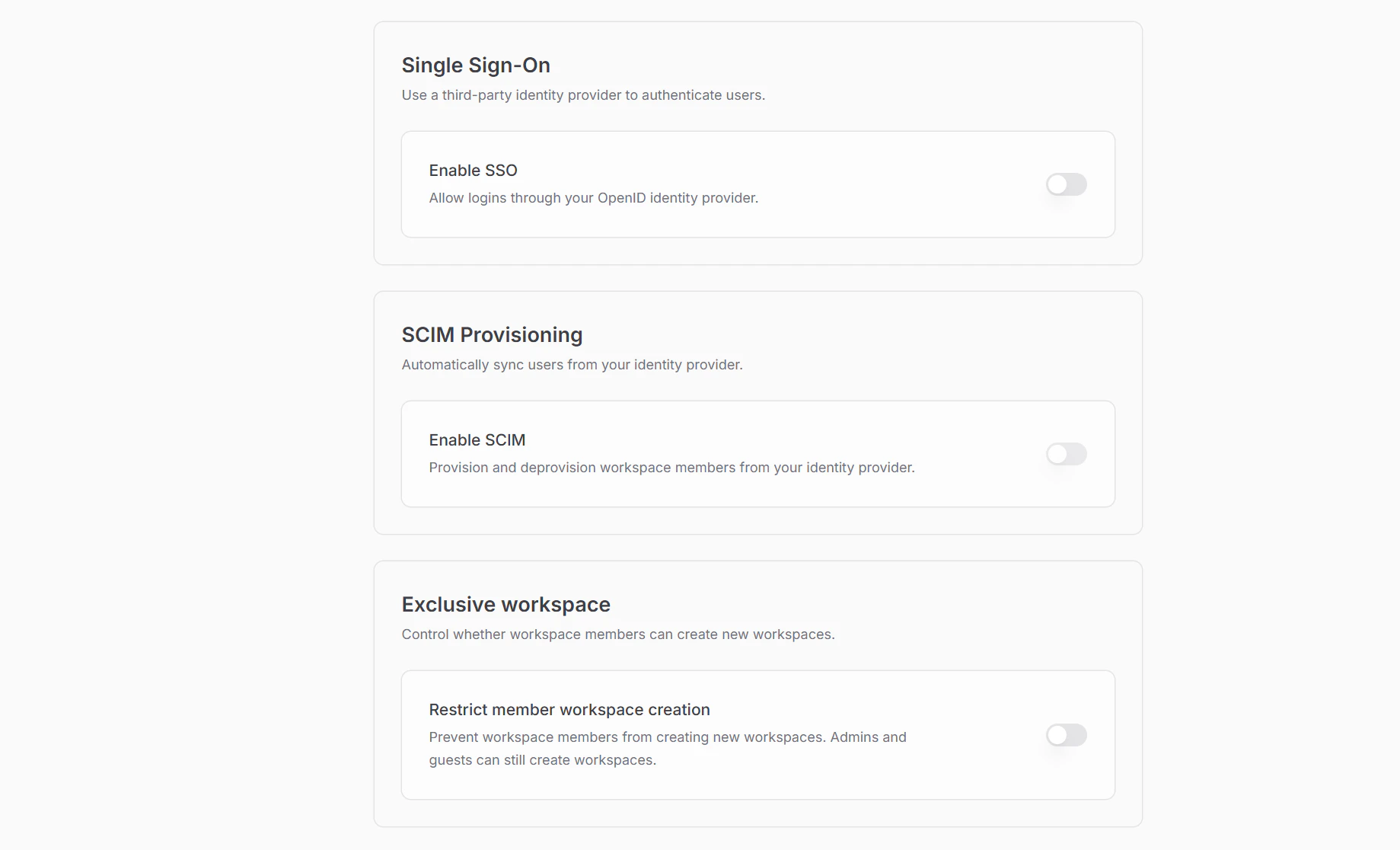
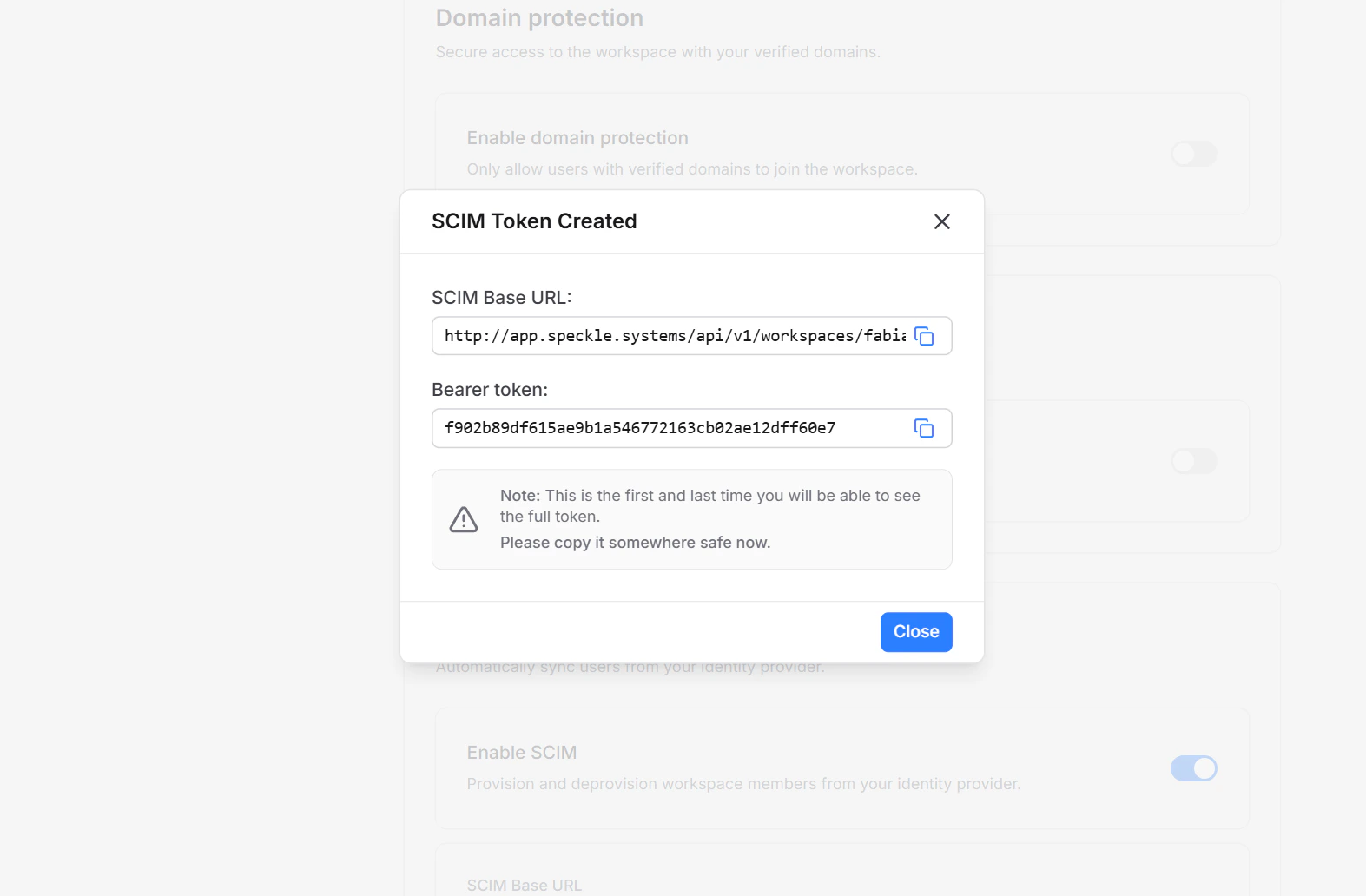
Generate a SCIM token
Click Enable SCIM. Speckle generates a workspace-scoped bearer token and shows it once in a reveal dialog. Copy the token and the SCIM base URL before closing.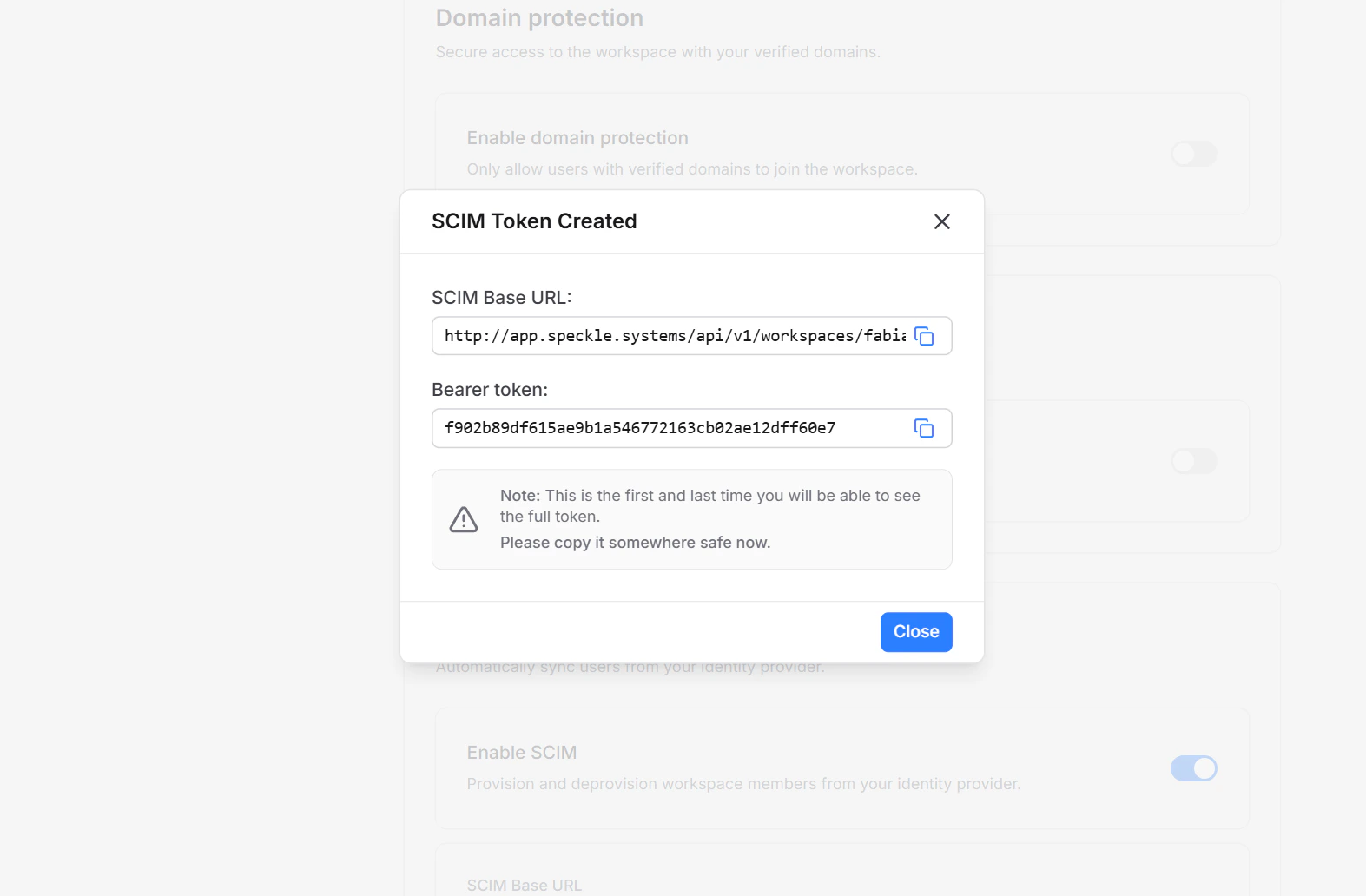
Configure your identity provider
In your identity provider, create a new SCIM 2.0 application pointing at: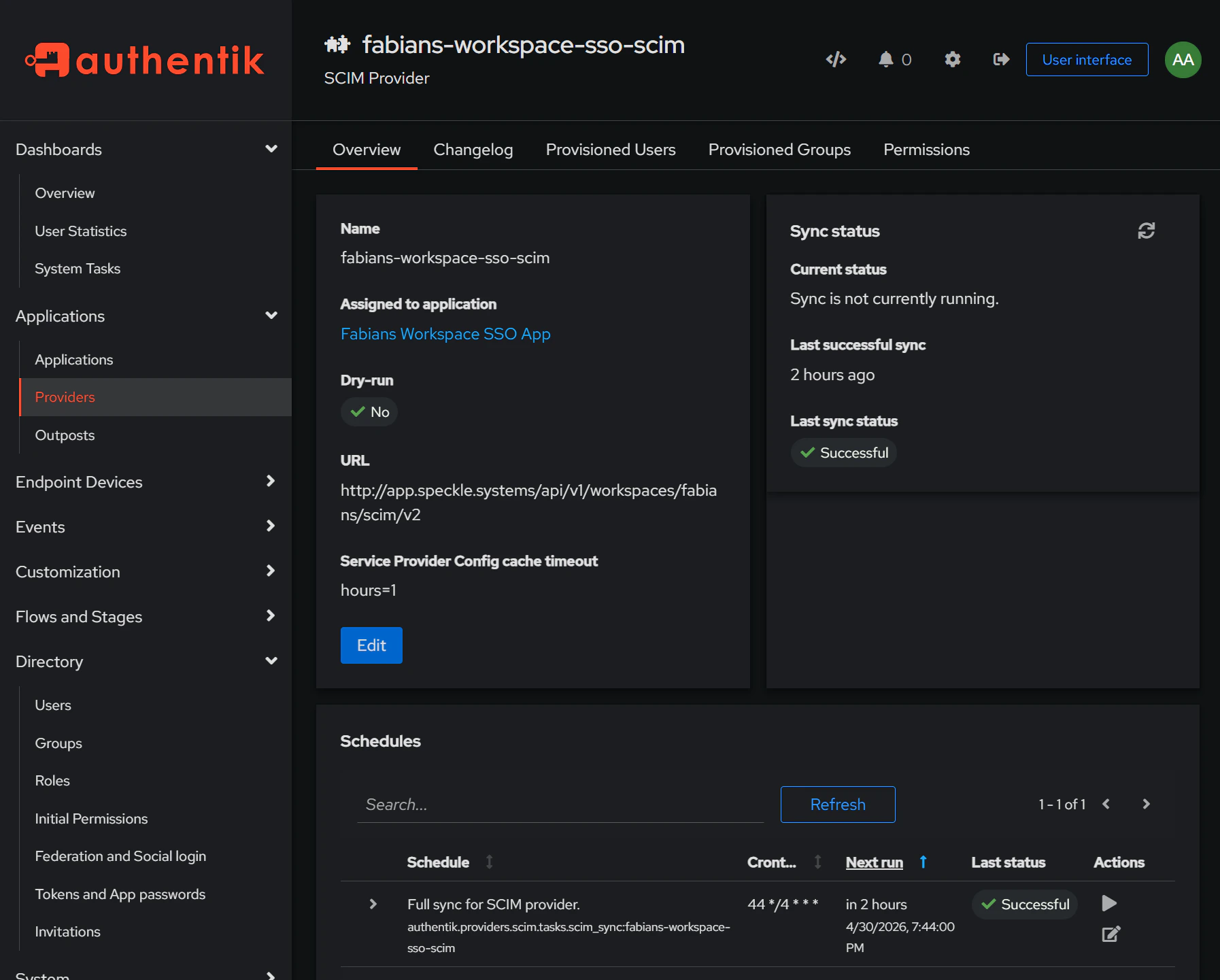
- SCIM endpoint: the base URL from the previous step, e.g.
https://app.speckle.systems/api/v1/workspaces/{workspace-slug}/scim/v2 - Authentication: bearer token (paste the token you copied)
member role.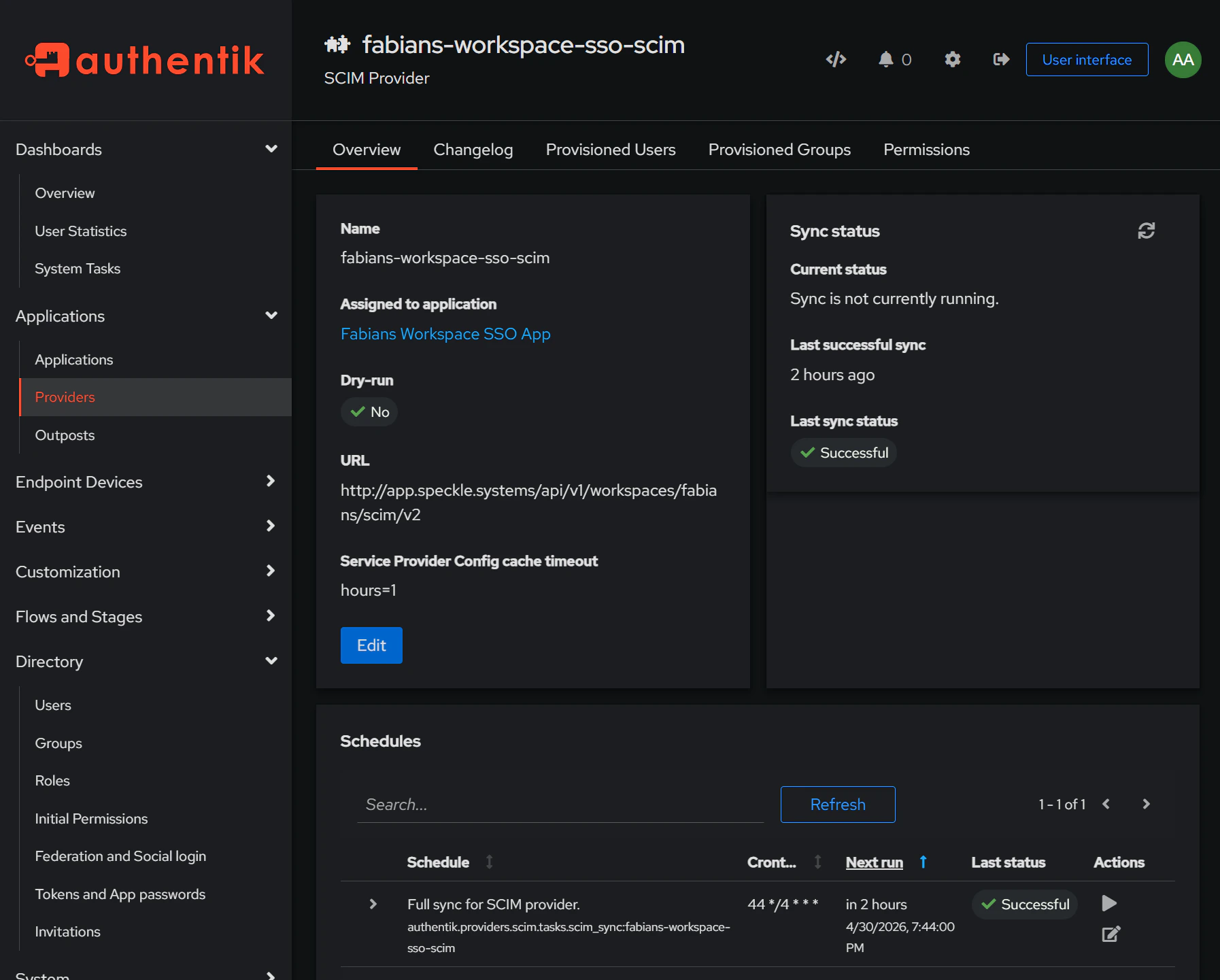
What SCIM syncs
When a user is provisioned
- A Speckle account is created if one doesn’t exist for the user’s primary email.
- An existing Speckle account is matched and linked when the email belongs to a verified workspace domain.
- The user joins the workspace as a
memberwith the default seat type. - The user’s display name and emails are synced from the identity provider.
When a user is updated
- Display name and given/family name updates flow through to the Speckle profile.
- Email changes on a verified workspace domain are synced. The identity provider’s primary email becomes the Speckle primary email.
- Secondary emails added in the identity provider are added in Speckle; secondary emails removed there are removed in Speckle.
- An unverified Speckle email matching the identity provider push is marked verified — Speckle trusts the identity provider as authoritative for its own domains.
Email sync is restricted to verified workspace domains. Personal emails (e.g.
@gmail.com) pushed from the identity provider are ignored.When a user is deprovisioned
- The user is removed from the workspace and their workspace seat is freed.
- Their Speckle account, projects, and other workspace memberships are untouched.
- Reactivating the user in the identity provider later restores their workspace membership with the default seat type and
memberrole.
Rotate or disable
Open the SCIM card menu:- Rotate token — generates a new token and revokes the old one. Update the token in your identity provider, otherwise the next sync returns 401.
- Disable SCIM — revokes the token and stops syncing. Existing workspace members are kept; manage them manually until SCIM is re-enabled.
SCIM endpoint reference
All requests useAuthorization: Bearer {token} and the application/scim+json content type. Pagination uses startIndex (1-based) and count.
| Endpoint | Methods | Purpose |
|---|---|---|
/ServiceProviderConfig | GET | Capability advertisement |
/ResourceTypes, /Schemas | GET | Schema discovery |
/Users | GET, POST | List (filter by userName eq or externalId eq), create |
/Users/{id} | GET, PATCH, PUT, DELETE | Read, update, deprovision |
/Groups, /Groups/{id} | GET (empty), other → 501 | Group provisioning is not implemented |
FAQ
Do I need SSO to use SCIM?
Do I need SSO to use SCIM?
Not strictly, but it is strongly recommended. SCIM provisions accounts but
does not handle login. Without SSO, every provisioned user must complete
Speckle’s password reset flow on first access. With SSO enabled first,
provisioned users sign in directly through your identity provider — no
password reset, no friction. Set up SSO before enabling
SCIM whenever possible.
What happens if a user's email is unverified in Speckle?
What happens if a user's email is unverified in Speckle?
SCIM returns a 409 conflict. Ask the user to verify their email in Speckle
(or remove the email from their account), then retry the sync from your
identity provider. SCIM never silently links unverified accounts.
Can SCIM change a user's password or other workspace memberships?
Can SCIM change a user's password or other workspace memberships?
No. SCIM never touches passwords — users authenticate through SSO
(recommended) or via Speckle’s password reset flow if SSO is not configured.
SCIM also only manages membership in the SCIM-enabled workspace; the user’s
other workspace memberships are untouched.
Can the same user be SCIM-managed in multiple workspaces?
Can the same user be SCIM-managed in multiple workspaces?
No. A user can only be SCIM-managed in one workspace at a time. Provisioning
a user who is already SCIM-active in another workspace returns a 409
conflict — deprovision them in the first workspace before provisioning
elsewhere.
What if I lose the SCIM token?
What if I lose the SCIM token?
Tokens cannot be recovered. Open Workspace Settings → Security, rotate
the token, and update your identity provider with the new value.
Does SCIM upgrade roles or seats above the defaults?
Does SCIM upgrade roles or seats above the defaults?
No. SCIM creates members on the workspace’s default seat type with the
member role. Promote users to admin or upgrade their seat manually in
Speckle.